Remote WorkForce VPN
Cloud-based VPN designed specifically for SMBs
Secure, scalable, and built for companies with distributed networks and remote teams

Experience modern cloud-based VPN the way it should be: effortless deployment, fortified security, limitless scalability, cloud-based, and compatible with all applications and devices. Our robust cybersecurity solution is tailor-made for SMBs.
Providing SMBs with enterprise-grade protection…without the complexity and exorbitant costs.
Encrypted communications for remote workers
Replace legacy VPNs with modern cloud-based VPN
Built for distributed network environments
Quick and frictionless startup
Remote WorkForce VPN is the culmination of a decade's worth of insights gleaned from safeguarding millions of customers globally.
BENEFITS
Why SMBs Choose Remote WorkForce VPN
Modern cloud-based VPN for the Remote Workforce
- Upgrade your legacy VPN with modern, cloud-based solution
- Enhance your on-line protection with Multi-Factor Authentication (MFA)
- Streamlined authentication with Single Sign-On (SSO)
- Comprehensive management reporting
- Malware protection against sources of viruses, phishing attacks, etc.


Effortless integration with existing IT infrastructure
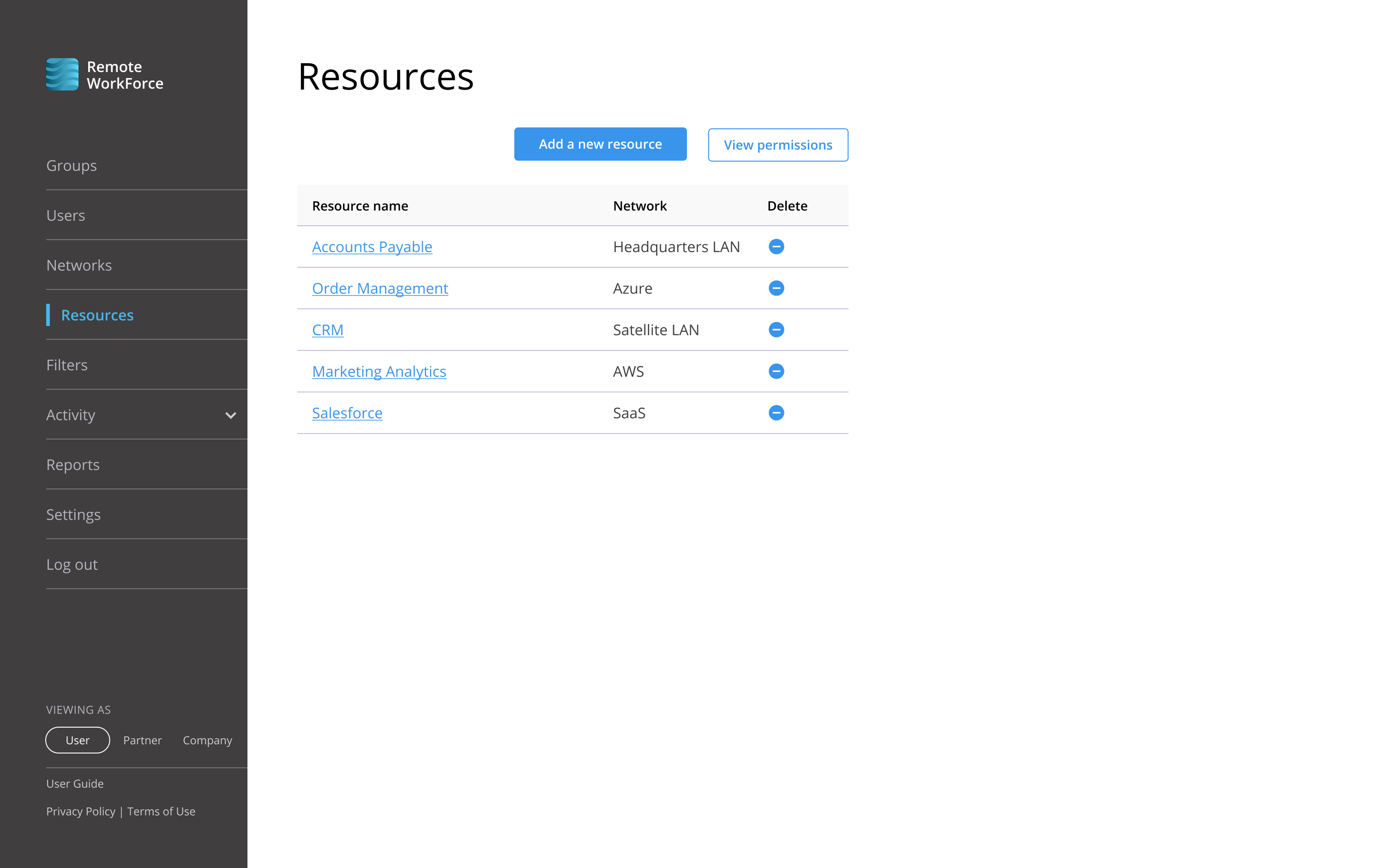
- Direct access to legacy LANs, cloud-based networks, and SaaS platforms
- End-to-end encryption for all user communications
- Support for both BYOD and company devices
- Available as Basic or Enhanced VPN. Easy upgrade to full ZTNA security.
Simple installation, provisioning, and usage
- Built specifically for SMBs
- Many companies can deploy and manage without an IT specialist involved
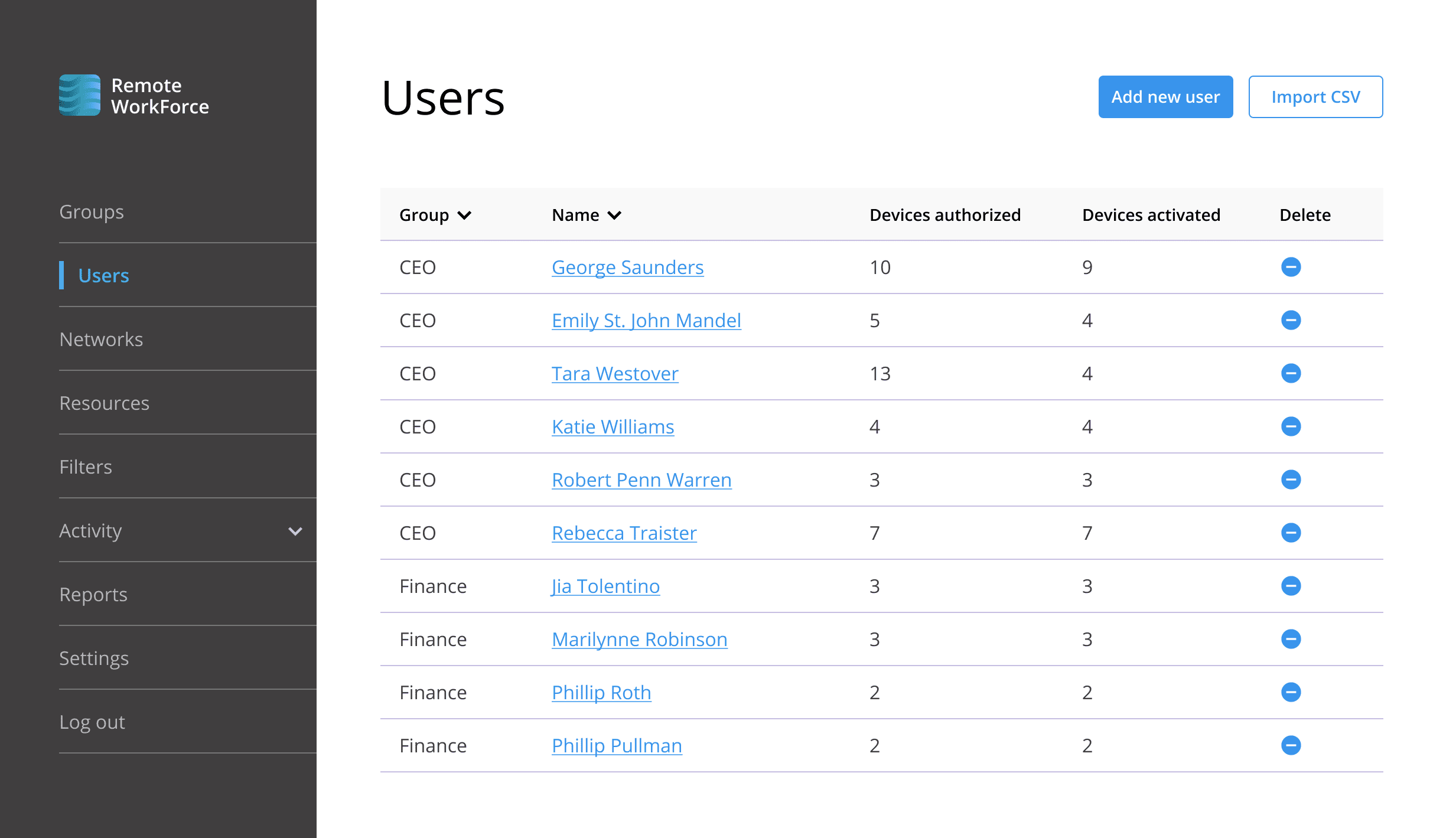
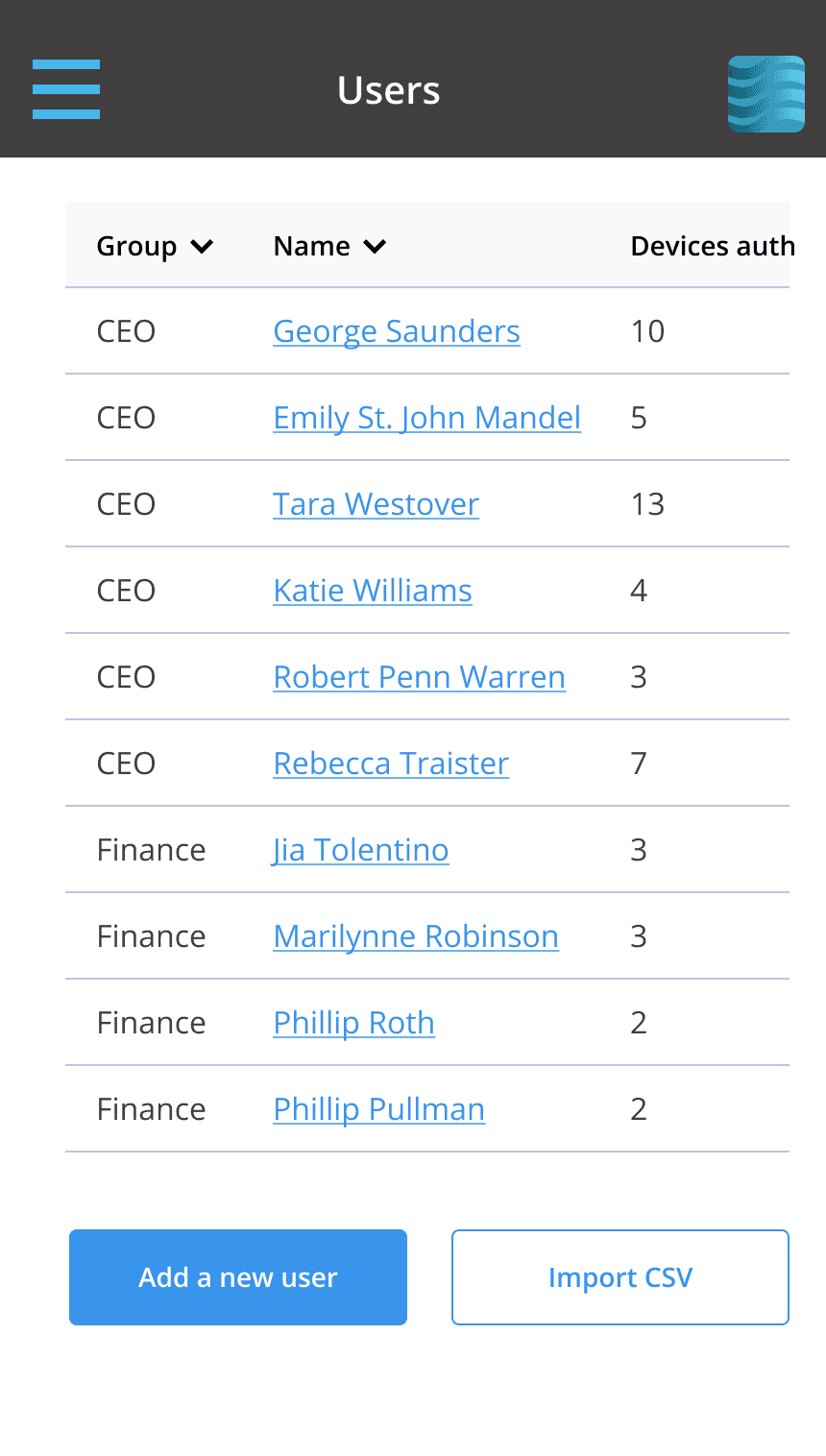
- Centralized control and reporting via an intuitive admin portal
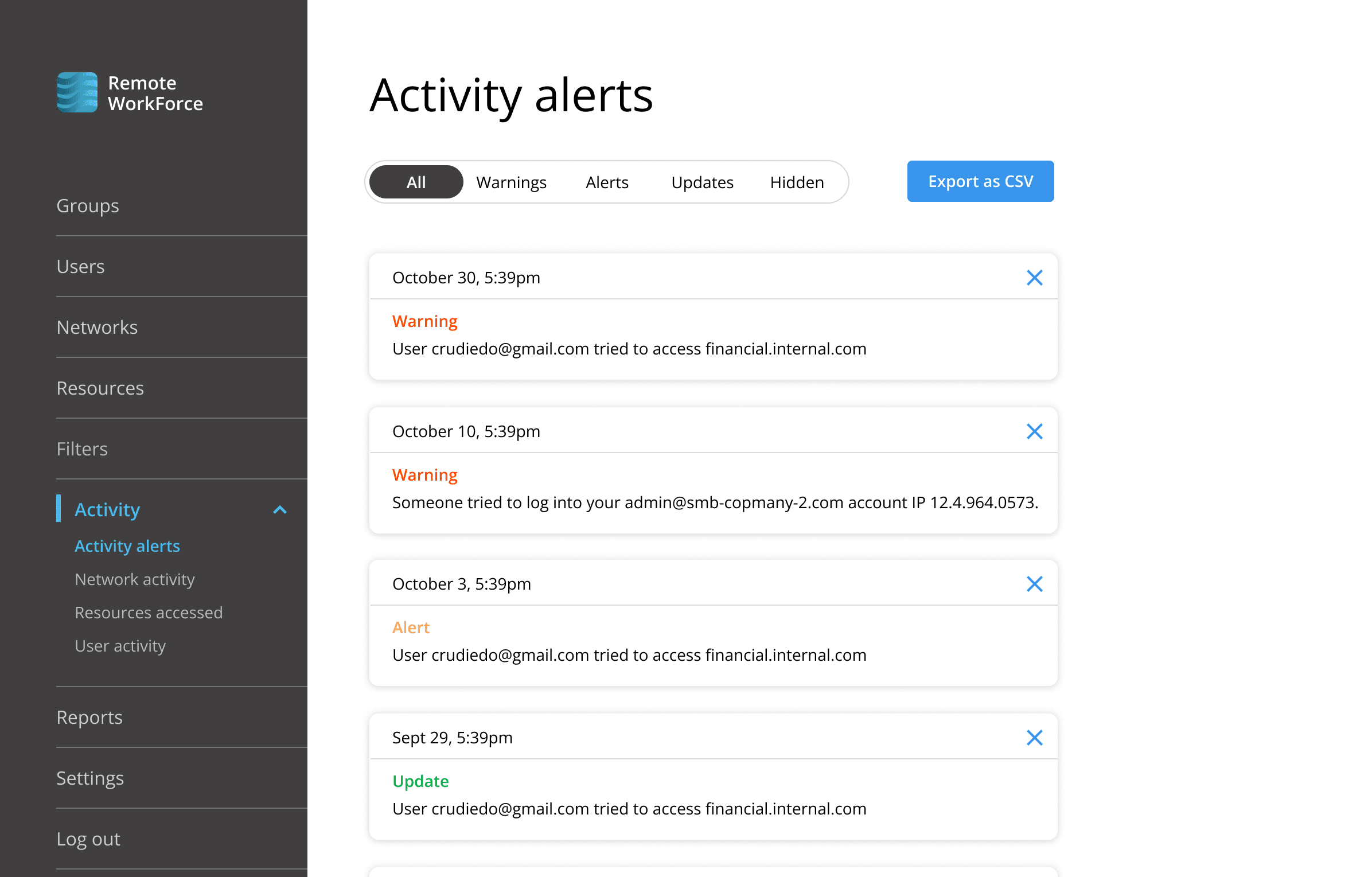
- Extensive, easy to access reporting of employee on-line activities, resources accessed, network utilization and security alerts.

Affordable and accessible
- Low per-user cost
- Flexibility with no startup costs, minimums, or fixed expenses
- Fully cloud-based solution. No hardware requirements.
- Replaces outdated VPN solutions
Compatible with
Laptops
- PCs
- Macs
Tablets and Smartphones
- iPhones
- iPads
- Android Phones
We are MSP friendly!
We provide:
- An easy-to-use service provider portal
- Excellent margins
- A user friendly experience means happy customers
And, we don’t sell directly.
Check out our MSP Corner to find out more about VPNs for SMBs and how to get started.
